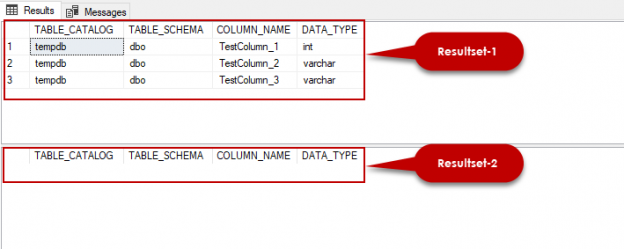
The SQL EXCEPT statement is one of the most commonly used statements to filter records when two SELECT statements are being used to select records.
The SQL EXCEPT statement returns those records from the left SELECT query, that are not present in the results returned by the SELECT query on the right side of the EXCEPT statement.
Read more »