Digital certificates are form of electronic authorizations used to verify the identities of persons, companies, computers, and other network entities.
Self-signed certificate
For those who are opt for some self-signed certificate, they must be aware that such a certificate can be used only for encryption, it will not provide any proof-of-identity for the server. As such, they are not recommended, especially when granting users permission to use an application via internet connection.
CA-signed certificate
SSL certificates are supplied by trusted third-party Certification Authorities (CAs). Depending on Certification Authorities, a certificate could be issued after just verifying the domain name, whereas some other authorities require to verify the business existence, who owns a domain name, and finally applicant credibility to apply for the certificate, thus ensuring a higher standard of authentication.
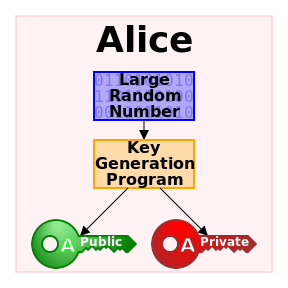
All web browsers come with a list of all well-known Certification Authorities. Along with the company and server name, a CA-signed certificate includes a server public key, used by the web browser to encrypt data sent to the server. A private key is also present on the server and the server uses that key to decrypt the data encrypted by the public key. A private key must be safekeeping on the server to prevent unauthorized access.
Additional information on public key cryptography can be found in the Public-key cryptography article.
More information about CA-signet certificates and how to obtain those can be found directly on some Certification Authorities web sites such as:
- SQL Server trace flags guide; from -1 to 840 - March 4, 2019
- How to handle the SQL Server WRITELOG wait type - June 13, 2018
- SQL Server performance counters (Batch Requests/sec or Transactions/sec): what to monitor and why - June 5, 2018